Beginner's Guide: How Azure Landing Zones Simplify Cloud Governance and Policy Management

Introduction
Navigating the world of cloud computing can feel overwhelming, especially when you're just starting out. You've probably heard terms like Azure Landing Zone, Cloud Governance, and Azure Policy, but what do they actually mean? How do they all fit together to create a secure and efficient cloud environment? If you've ever asked these questions, you're in the right place!
At AllThingsCloud, we believe learning should be fun and accessible. That's why we've enlisted our expert mentor, Truffle, to guide our new apprentice, Paula, through the fundamentals of Azure Landing Zones.
Paula, just like many of you, is curious and eager to learn. She recently asked, "Truffle, what exactly is an Azure Landing Zone?"
Truffle, with a friendly and commanding smile, replied, "Great question, Paula! A landing zone is a pre-configured Azure environment following best practices!"
This simple exchange is the start of a journey into one of the most critical concepts in the Microsoft Cloud Adoption Framework. An Azure Landing Zone isn't just a buzzword; it's the foundational blueprint for building a secure, scalable, and operationally excellent cloud estate. It ensures that from day one, your environment is ready for your workloads, with proper Cloud Governance and security controls in place.
In this post, we'll follow Truffle and Paula as they explore the eight critical design areas of an Azure Landing Zone. From identity and networking to security and automation, you'll see how everything interconnects. Let's dive in!
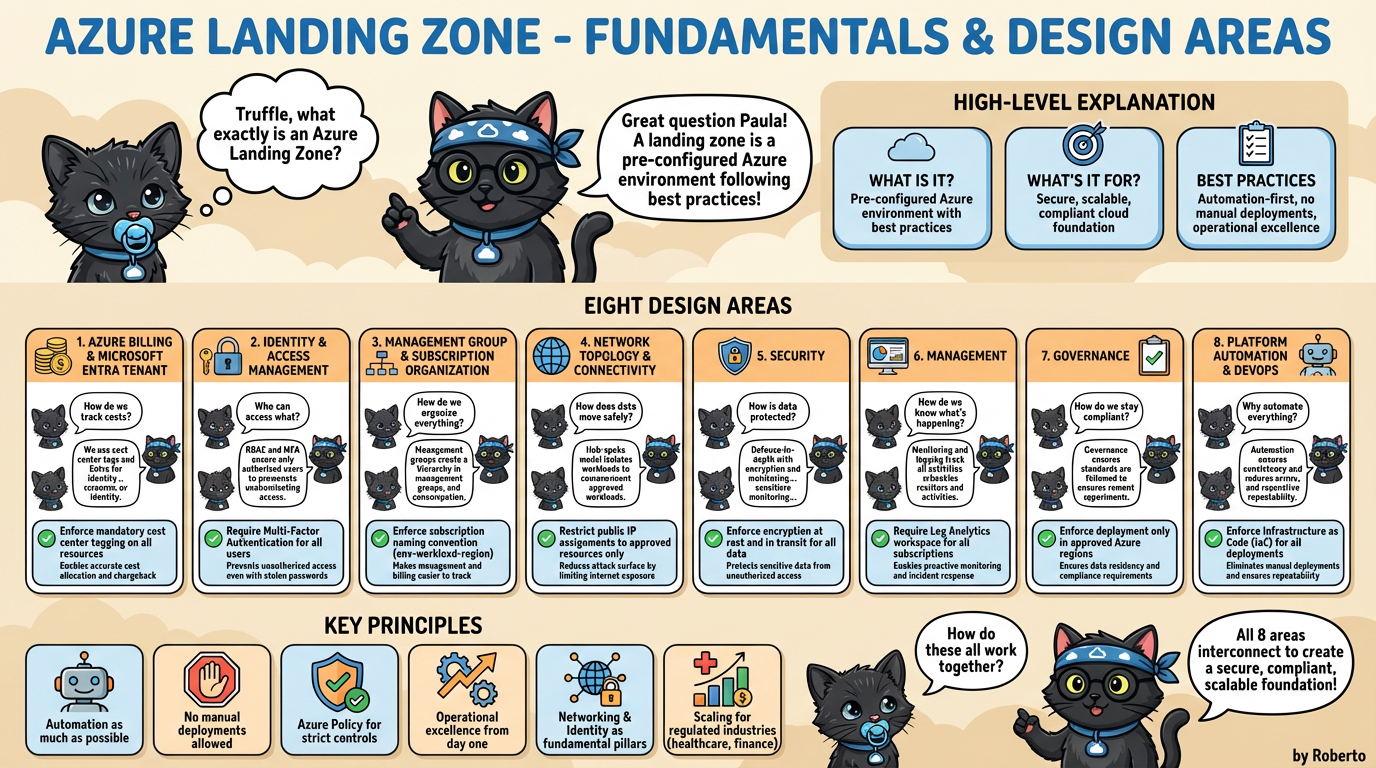
Exploring the 8 Design Areas of an Azure Landing Zone
Now that we have a high-level overview, let's break down each of the eight design areas. Truffle will guide us through each one, answering Paula's insightful questions along the way.
1. Azure Billing and Microsoft Entra Tenant
Paula kicked things off with a practical question: "How do we track costs?"
Truffle explained, "We use cost center tags and Microsoft Entra ID for identity."
This first area is all about the financial and identity foundation. Before you can build anything, you need to know how you'll pay for it and who will have access. An Azure Landing Zone establishes a clear billing structure and connects it to a single Microsoft Entra ID (formerly Azure Active Directory) tenant. This tenant acts as the identity provider for your entire organization, ensuring that user access is managed centrally.
The Role of Azure Policy: The policy example here, "Enforce mandatory cost center tagging on all resources," is crucial for Cloud Governance. It automatically ensures that every resource deployed (like a VM or storage account) is tagged with a cost center. This makes it easy to track spending by department, project, or environment, preventing budget overruns.
2. Identity and Access Management (IAM)
Paula naturally followed up with, "Who can access what?"
"RBAC and MFA ensure only authorized users have access," Truffle clarified.
IAM is the security gatekeeper of your cloud environment. This design area focuses on implementing strong authentication and authorization controls. Role-Based Access Control (RBAC) is used to grant permissions based on a user's role (e.g., developer, database administrator), following the principle of least privilege. Multi-Factor Authentication (MFA) adds a critical layer of security, requiring users to provide a second form of verification.
The Role of Azure Policy: The policy, "Require Multi-Factor Authentication for all users," is a powerful security measure. It programmatically enforces the use of MFA across your organization, significantly reducing the risk of unauthorized access from compromised credentials.
3. Management Group and Subscription Organization
"How do we organize everything?" Paula wondered, looking at the scale of the cloud.
Truffle pointed to a diagram, "Management groups create a hierarchy for our subscriptions."
As your organization adopts the cloud, you'll likely have multiple subscriptions for different environments (production, development) or departments. This design area provides a logical structure for managing them. Management Groups allow you to group subscriptions together and apply governance policies and access controls to all of them at once, creating a clean, hierarchical, and manageable structure.
The Role of Azure Policy: Enforcing a consistent "subscription naming convention" might seem small, but it's vital for operational excellence. This policy ensures that every subscription is named logically (e.g., prod-webapp-australiaeast), making it instantly clear what its purpose is.
4. Network Topology and Connectivity
Paula’s next question was about data flow: "How does data move safely?"
"A hub-spoke network model isolates workloads and controls traffic," Truffle explained.
Networking is a fundamental pillar of any landing zone. This area defines the network architecture. The recommended approach is a hub-spoke topology, where a central "hub" virtual network handles external connectivity and shared services (like firewalls), and individual "spoke" networks host your application workloads. This model provides network isolation, enhances security, and simplifies management.
The Role of Azure Policy: The policy to "Restrict public IP assignments" is a critical security control. By limiting which resources can be exposed directly to the internet, you dramatically reduce your environment's attack surface, forcing traffic through controlled pathways like firewalls and gateways.
5. Security
"How is our data protected?" Paula asked, concerned about sensitive information.
"We use a defense-in-depth strategy with encryption and continuous monitoring," Truffle assured her.
This design area brings together all aspects of security. It's not just about one tool but a multi-layered approach. This includes encrypting data both at rest (in storage) and in transit (over the network), implementing threat detection with services like Microsoft Defender for Cloud, and ensuring you have a comprehensive view of your security posture.
The Role of Azure Policy: The policy to "Enforce encryption at rest and in transit" is non-negotiable for Cloud Governance. It ensures that data stored in Azure SQL or Azure Storage is automatically encrypted, and that traffic to these services uses secure protocols like HTTPS, meeting most compliance requirements by default.
6. Management
"How do we know what's happening in our environment?" Paula inquired.
"Monitoring and logging track all activities, giving us full visibility," Truffle responded.
Effective management is key to operational excellence. This design area focuses on monitoring, logging, and automation. By centralizing logs from all your resources into a Log Analytics workspace, you gain deep insights into the health, performance, and security of your applications. This enables proactive alerting, automated responses to issues, and detailed forensic analysis when needed.
The Role of Azure Policy: Requiring a "Log Analytics workspace for all subscriptions" ensures that no resource is left unmonitored. This policy automatically configures logging, providing a complete audit trail for security and compliance.
7. Governance
Paula, thinking about rules and regulations, asked, "How do we stay compliant?"
"Governance ensures our standards are followed automatically," Truffle stated.
While governance is woven through all design areas, this one focuses on the tools that enforce it. Azure Policy is a cornerstone of this, but it also includes using Azure Blueprints to package and deploy compliant environments and managing costs with Azure Cost Management. The goal is to ensure your cloud environment adheres to both internal corporate standards and external regulatory requirements.
The Role of Azure Policy: The policy to "Enforce deployment only in approved Azure regions" is essential for organizations with data residency requirements (like those in finance or government). It prevents accidental or malicious deployment of resources in non-compliant geographic locations.
8. Platform Automation and DevOps
Finally, Paula asked, "Why do we need to automate everything?"
"Automation ensures consistency, reduces human error, and makes us faster and more reliable," Truffle concluded.
This final design area is about embracing an automation-first mindset. Manual deployments are slow, error-prone, and inconsistent. An Azure Landing Zone promotes the use of Infrastructure as Code (IaC) tools like ARM templates, Bicep, or Terraform. This allows you to define your entire infrastructure in code, enabling repeatable, automated, and version-controlled deployments through a DevOps pipeline.
The Role of Azure Policy: Enforcing "Infrastructure as Code (IaC) for all deployments" is an advanced but powerful governance control. It can be implemented by restricting direct portal deployments for production environments, forcing all changes to go through a validated and audited DevOps pipeline.
Conclusion
Building a robust cloud environment is about more than just deploying virtual machines and databases. It's about creating a solid foundation that supports growth, ensures security, and maintains compliance. The dialogue between Truffle and Paula has shown us that a well-designed Azure Landing Zone is the key to achieving this.
We've covered the eight critical design areas and seen how principles like automation, operational excellence, and the strategic use of Azure Policy come together to enforce Cloud Governance. But the real power of a landing zone shines when applied to real-world scenarios.
Paula was curious about this too, asking, "This sounds great, but how does it protect real data?"
Truffle's answer lies in our second infographic, which details how an Azure Landing Zone protects highly sensitive information in regulated industries like healthcare and banking, adhering to strict Australian compliance standards like the Privacy Act, APRA CPS 234, and the Health Records Act.
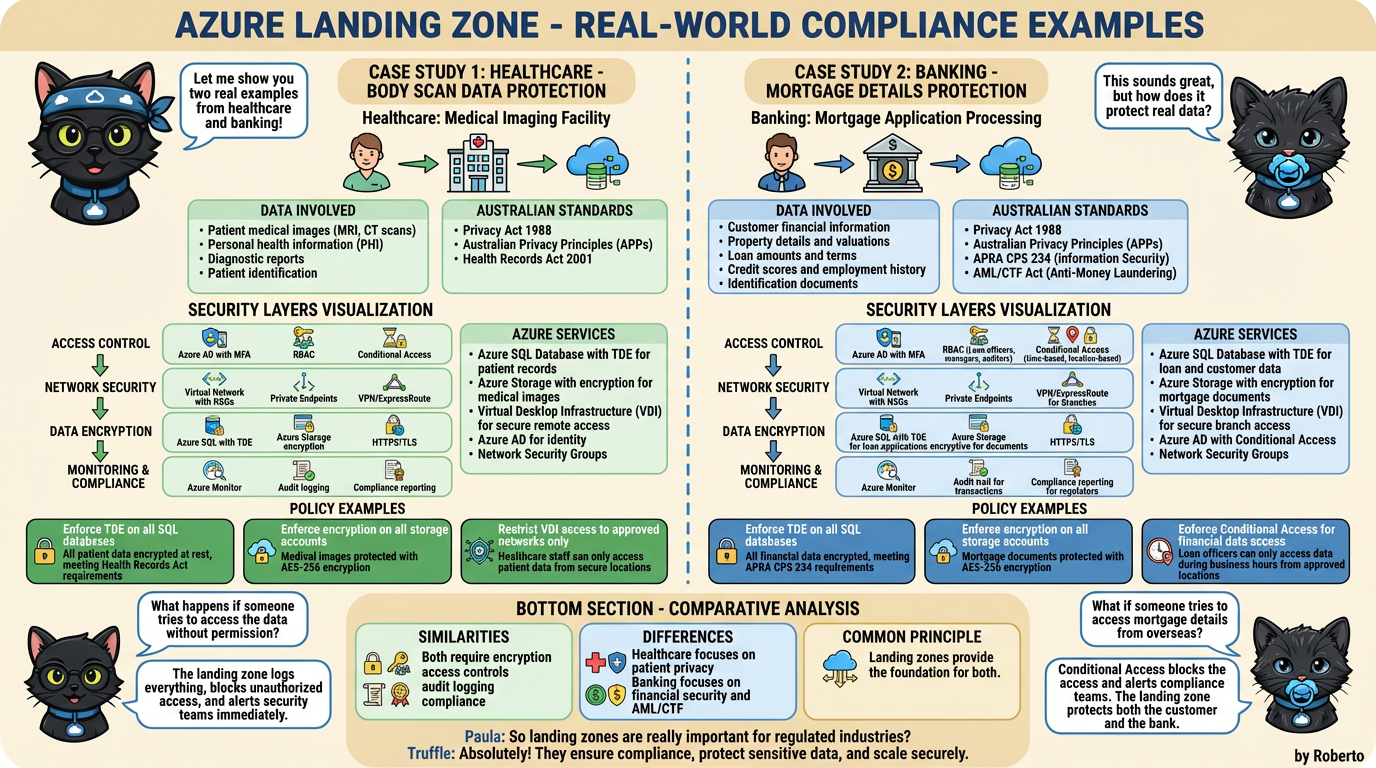
In the end, Paula's final question summed it all up: "So landing zones are really important for regulated industries?"
And Truffle's response is the ultimate takeaway for every cloud professional: "Absolutely! They ensure compliance, protect sensitive data, and scale securely."
By starting with a properly configured Azure Landing Zone, you're not just building for today; you're creating a future-proof platform that enables innovation while keeping your organization and its data safe.
What are your thoughts on Azure Landing Zones? Do you have any questions for Truffle and Paula? Share your comments below!